Learning On Alison Is Easy
We believe that empowering yourself should be rewarding, simple, and free. That's why your journey from choosing a course to getting the certificate for it takes only 6 easy steps. Check them out below!
We believe that empowering yourself should be rewarding, simple, and free. That's why your journey from choosing a course to getting the certificate for it takes only 6 easy steps. Check them out below!



Yes, our certificates have helped people all over the world to achieve their dreams. Our graduates tell us how we have helped them in their careers and personal lives. Check out their testimonials here.
Absolutely! All our courses are CPD UK accredited and taught by subject matter experts, including many university lecturers. Our courses consistently receive good ratings on platforms such as Trust Pilot , Facebook and Google Play.
Many people tell us that they have got jobs or progressed further in their careers with the help of Alison. By pursuing online learning, you are not only adding to your skills and knowledge, but you’re also showing potential employers that you’re a positive go-getter and keen to learn.
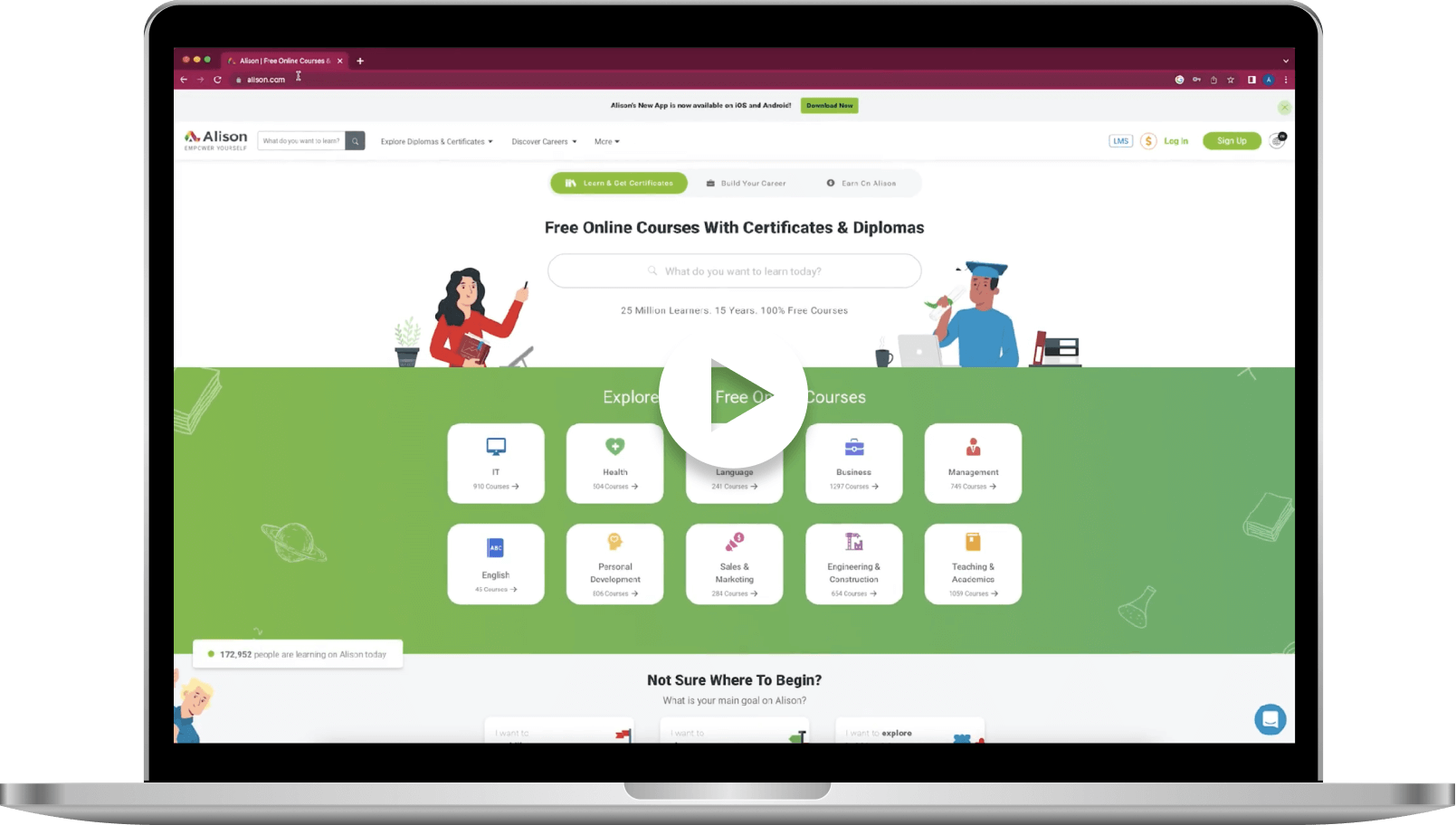
Alison’s courses fall into three study areas: academic, workplace, and personal development. You can find everything from cybersecurity and artificial intelligence to massage and tattoo art.
It’s completely free to take all our courses and if you pass the assessment you can opt to buy a printed or PDF certificate or diploma for a nominal fee. If you don’t wish to purchase a certificate or diploma but want to prove that you have completed a course, you can download your free learner record .
The beauty of online learning is that you can complete our courses in the time that suits you. For complicated subjects, you can retake a lesson as often as you like. Our certificate courses are designed to be completed in about three hours while diploma courses take approximately 15 hours. You can retake the assessment as often as you need to to achieve the 80% pass rate.
We’re for you, wherever you are and whatever you need. Our free online courses cater to everyone, no matter your age or interests.
With over 4,000 courses on Alison and more being added every week, that is a tricky question. Alison has in-demand free online courses in health, business, skilled trades, HR, marketing, teaching, hospitality and many more. Here are a few suggestions for you:
Diploma in Nursing and Patient Care
Elderly Care and Caring for the Disabled
Caregiving Skills - Dementia Care
Diploma in Human Resources (HR)
Diploma in Operations Management (Ops)
Diploma in Business Administration
Basics of Manual Handling in the Workplace
Diploma in Workplace Safety and Health
Diploma in Teaching Skills for Educators
Mental Health Studies - Suicide, Violent Behavior and Substance Abuse
Fundamentals of Domestic Violence and Abuse
ISO 9001:2015 - Quality Management System (QMS)
You simply register for your free account and enrol in the course of your choice - it’s that easy. You can download the app and continue studying on your phone. Our customer support team is always available to help you with any technical issues.
Apart from providing free online lessons to the whole world, Alison also offers learners the opportunity to earn while you learn. Join our Affiliate programme and you will receive 20% of the revenue generated by new learners that you bring to the website. We also offer a free Personality Test that can help you decide where your strengths lie, a comprehensive Career Guide to help you plan your future and a Resumé Builder so that you can create a professional-looking CV. Last but not least, our free Wellbeing Assessment will show you how to achieve greater fulfilment in your career.